Plus a fresh exploit from Nightmare Eclypse.
Read the full storyThe Stack
Interviews, insight, intelligence, and exclusive events for digital leaders.
All the latest
All the latest
4342 Posts
|
AI
|
Jun 10, 2026

Anthropic's Red Team tells defenders Mythos Preview can serve up N-days in hours, not weeks.
Jun 10, 2026
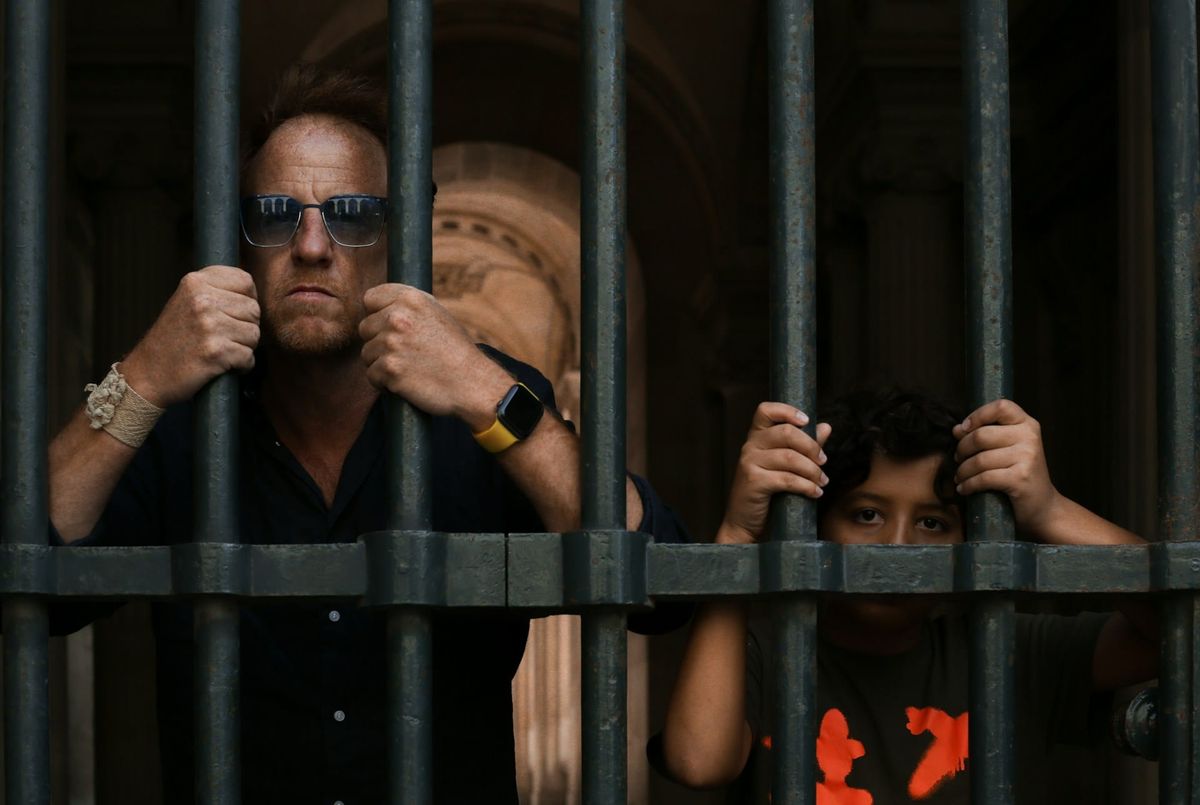
High-profile cyber incidents are forcing boards to take security more seriously. But CISOs still need to balance the business strategy with basic defensive measures, and demands for resilience.