Greg Linares’ new electronic dance music (EDM) album “VX” was made with malware – quite literally.
Back in the late 1990s Linares’ two loves were making electronic music and writing computer viruses.
He’s now a white hat working in cybersecurity for an investment firm but continues to make music – by extracting data from malware and code in order to make sounds that he assembles into dance tracks.
Linares releases his album for download under an open source license (CC BY-SA) this week. It includes songs built on over 200 malware samples including everything from late 90s classics through to things like REvil and Stuxnet.
He told The Stack that the album "uses code, images, network traffic, and entropy values of malware to make up the sounds, note patterns and efx" of the album -- something the single dad describes as "a throwback out of respect to my roots and all the virus authors who did the ‘black arts’ of virus writing in the 90s."
(Writing viruses was an "autistic interest" he says before he then "found the scene on irc... I was fascinated by them and it was like a family to me" he says -- he was in groups NuKE, SLAM and Team Necrosis.)
We caught up with Linares, who goes by "Laughing Mantis" to learn more (lightly edited for clarity.)
Where did the idea of making music with malware come from?

“I got the idea [of combining these interests] about seven years ago when I was reverse engineering a piece of malware called Careto and noticed the assembly code MOV values looked similar to how a beat lines up in a DAW (digital audio workstation) step sequencer.
"Being the neurodivergent geek that I am, I decided to map each assembly code command to a drum channel and make patterns based on what was disassembled from the Careto malware sample I had. Luckily for me it actually made a pretty solid 4/4 techno beat.”
How hard is it/what tools did you use?
It is extremely hard and probably the most inefficient way to make music ever. It's like using those text to image AI generation tools but only being able to type one word in the prompt while the next three words are randomly typed in by a drunk monkey. Making a song using this method you are completely at the mercy of data and however you map the data in order to make ‘music’. Quite honestly most of the time when I make music like this it is closer to fuzzing software for vulnerabilities than making traditional music.
Pop The Stack a follow on LinkedIn here
"Since this original primitive method I have expanded quite a few different ways to extract data from malware and code in order to make sounds. The first method, which I called x86 transcoding, would generally be only good for rhythms and drums. I then experimented with turning letters of strings in code, tweets, and malware into Morse code values and then using the dots and dashes themselves as signals to send to notes. This would generate a lot of the rhythm patterns and even some melodies on the latest album as well."
"Another method I used was using the entropy values of malware as audio waveforms to be used in a synthesis technique called wavetable synthesis. Basically by mapping the values of the randomness in a malware code section and then using those values to draw a sound waveform I was able to actually generate sound from a piece of malware using data. For this project the use of a Novation Nova’s wavetable drawing and the creative freedom of the Waldorf Kyra and Iridium’s engines were critical for making most of the sounds on the album."
What malware are we listening to on this album?
"The VX album has over 200 malware samples used to make synthesizer sounds, drum beats, sound effects, arpeggios, and LFO modulations. Some of the highlights of the album are rare pieces of malware from the 90s virus writing groups 29A, NuKE, SLAM, No Mercy, Team Necrosis and Metaphase.
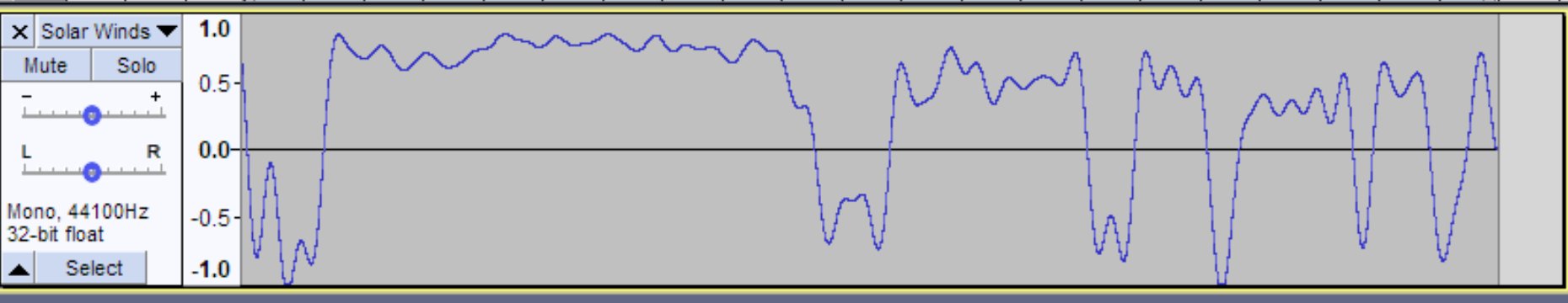
"As well as modern day ransomware and malware tools samples from REvil, Conti, Lapsus$. One of the tracks was made exclusively from early 2000s remote access trojans like NetBUS, Sub7, and Back Orifice 2k. The second part of this album, which will be released around Christmas time will have a few interesting historical malware pieces such as Solar Winds, Duqu and Disk Wiper.
How challenging was it getting the album finished and mastered?
"[It was] not nearly as nerve-wracking as how many times my DAW has crashed for this album. I looked back in my error log folder and I had around 483 crashes since I started this album. That equated to about three lost tracks and so many hours lost of production time. The album had to be split into two because of how unstable rendering and music development became. I am gonna take the next few weeks to rebuild my system and recode several of the tools I made. As for mastering, I did all of the engineering and mastering myself this time around."
What does the title "VX" refer to?
It's short for “Virus eXchange“ an old reference to 1990s computer virus-writing scene.
Why open source it?
"Honestly one of my dreams is to have my music in video games, game soundtracks along with bands like The Prodigy, Juno Reactor, Velvet Acid Christ, Numb and Frontline Assembly were my biggest source of inspiration to make music in the 90s. I did manage to have my music featured in The Matrix sequels as well one of the trailers of the Matrix MMORPG back in the day. The closest to being featured in an actual video game was getting hired by a third-party who was helping with the Starcraft Ghosts sound and music - only to be laid off two weeks into my job. By open sourcing my music to be used everywhere for free I really hope streamers, game studios and other artists can use my music for their content. That sounds infinitely better than being a signed musician again."








