
The US's Cybersecurity and Infrastructure Security Agency (CISA) has updated its list of actively exploited vulnerabilities -- bugs in firewalls from Taiwan's ZyXEL and VMware's Spring Cloud Gateway joining May's additions from Apple, Microsoft, F5 and OpenSSL among the 662-strong list of attacked software flaws.
CVE-2022-30525, a pre-authentication, command injection vulnerability leading to full remote code execution (RCE) in numerous Zyxel firewall versions. It has a CVSS score of 9.8 and was reported by Rapid7.
Zyxel firewall vulnerability: Tens of thousands believed exposed
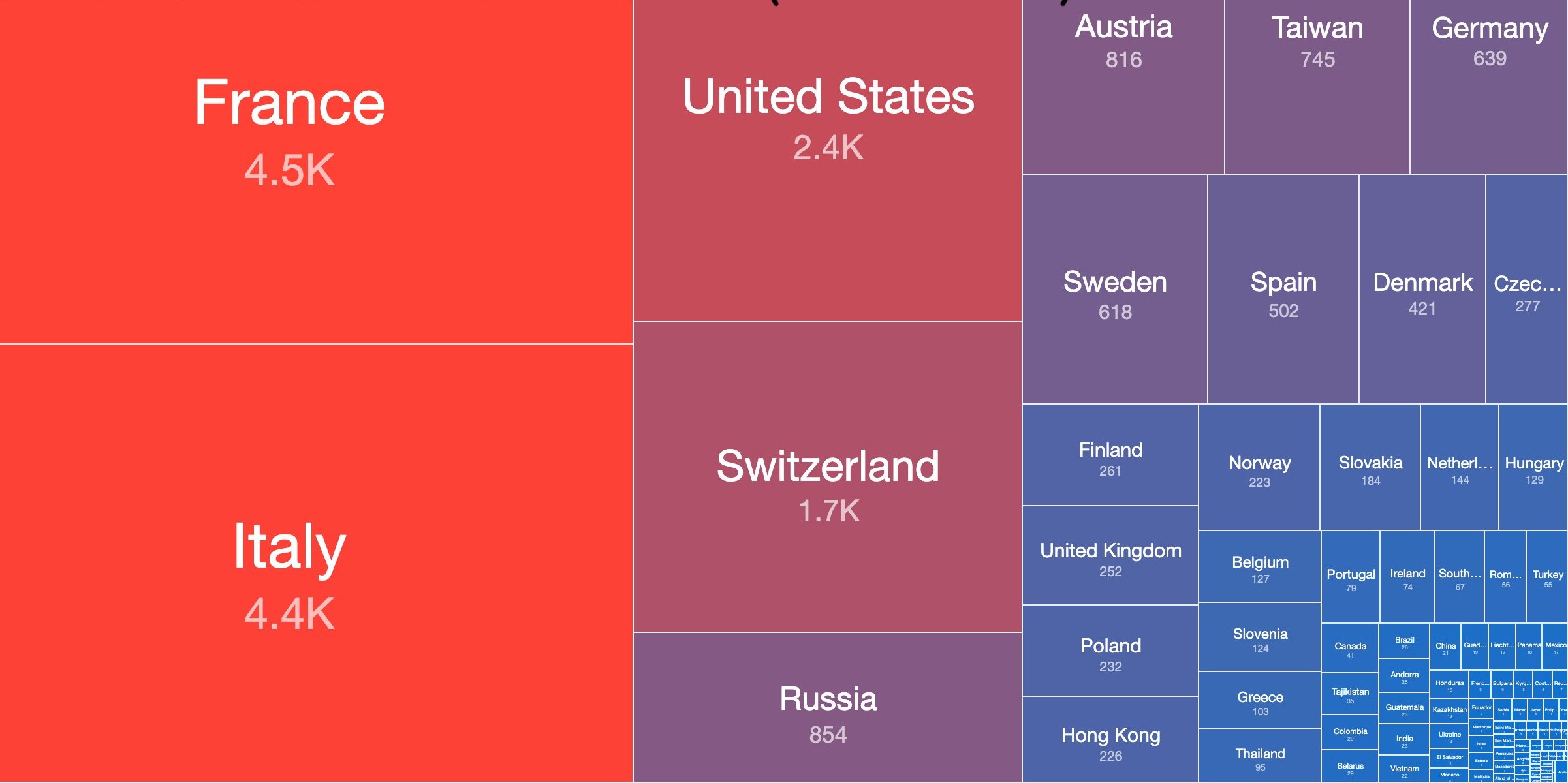
Zyxel pushed a patch on April 28 but exploits have circulated widely. As of May 13, there were still 20,800 potentially affected Zyxel firewall models (by unique IP) on the Internet according to Shadowserver data, shown left.
CVE-2022-22947 meanwhile is a CVSS 10-rated pre-auth RCE in VMware's Spring Cloud Gateway (a library for building API gateways on top of Spring and Java). This vulnerability was reported by security researcher Wyatt Dahlenburg, whose detailed write-up and proof-of-concept is here. The vulnerability is already being abused by a new variant of the Sysrv botnet, known for exploiting vulnerabilities in web apps and databases to install coin miners on both Windows and Linux systems.
https://twitter.com/MsftSecIntel/status/1525158219206860801
Both of the above two vulnerabilities were added to CISA's database on May 16.
BIG-IP vuln: F5 implores users not to put TMUI on public internet
Another recent addition (May 10) is CVE-2022-1388, the CVSS 9.8 pre-auth RCE in F5's BIG-IP suite of gateway/firewall services covered by The Stack here. As with so many critical vulnerabilities it took less than 48 hours for security researchers to work out how to exploit this CVE after F5 posted its advisory on May 6 and start sharing details on how to do so -- many emphasising that it was "trivial" to abuse.
BIG-IP's suite variously lets users manage cloud, virtual, and physical infrastructure, track the dynamic performance levels of servers, the state of network sessions, decrypt SSL traffic to identify potentially hidden attacks, distribute DNS and user application requests based on business policies etc. or operate as firewall.
This particular new vulnerability has attracted a lot of negative attention: not least because it is in the same BIG-IP component vulnerable to another RCE vuln last year, CVE-2021-22986. The bug lies in /mgmt/tm/util/bash -- an API operation on the management interface of the F5 devices.
It rapidly attracted (of course unprovable) accusations of being an intentional backdoor -- one early commentator telling us more sceptically that it was "likely there for management purposes, expected to be called with authentication and inadvertently exposed from an external perspective.
They added: "Due to the simplicity of the vulnerability, I would have expected it to have been identified through routine penetration testing performed by the vendor, but it slipped the net..."
Three pre-authentication RCE vulnerabilities in a flagship security product in 24 months is not a good look (one was one of 2020's most-exploited vulns.) The Stack asked F5 what it was doing to improve QA: "We have comprehensive security practices across the company, which we are constantly reviewing to ensure we are meeting ever-evolving cybersecurity threats" a spokesperson said: "We are focused on driving improvements in our processes and procedures to further enhance our products and security practices. We have evolved areas across the company, from secure training and secure development frameworks, to penetration testing, internal and external auditing, and vulnerability management and disclosure. We further strengthen our security measures through close collaboration with third parties who regularly perform diligence on and test our systems. We also provide detailed guidance for securing BIG-IP and strongly advise customers never to expose their BIG-IP management interface (TMUI) to the public internet and to ensure the appropriate controls are in place to limit access.
Readers can subscribe to CISA's "Known Exploited Vulnerabilities Catalog Update Bulletin" here. Be warned that owing to the speed of patch reverse engineering, POC sharing et al, additions to it often happen after automated scanning has happened, so if it is your first alert that you are exposed and unpatched, assume compromise.
