
Outsourcing colossus Serco has been hit by ransomware, with the "BABUK" crew claiming to have been inside networks for three weeks before activating the payload -- and to have copied "more than 1TB" of data.
Serco employs over 50,000 people and operates across Defence, Justice & Immigration, Transport, Health and Citizen Services. It generates over £3 billion in revenues annually and is led by Rupert Soames, a grandson of Winston Churchill and brother of Conservative politician Nicholas Soames.
"Serco’s mainland European business has been subject to a cyber-attack. The attack was isolated to our continental European business, which accounts for less than 3% of our overall business. It has not impacted our UK business or the services that we deliver for our UK customers" Serco said, in a statement that may not assuage European customers.
Serco hacked: "BABUK" takes responsibility.
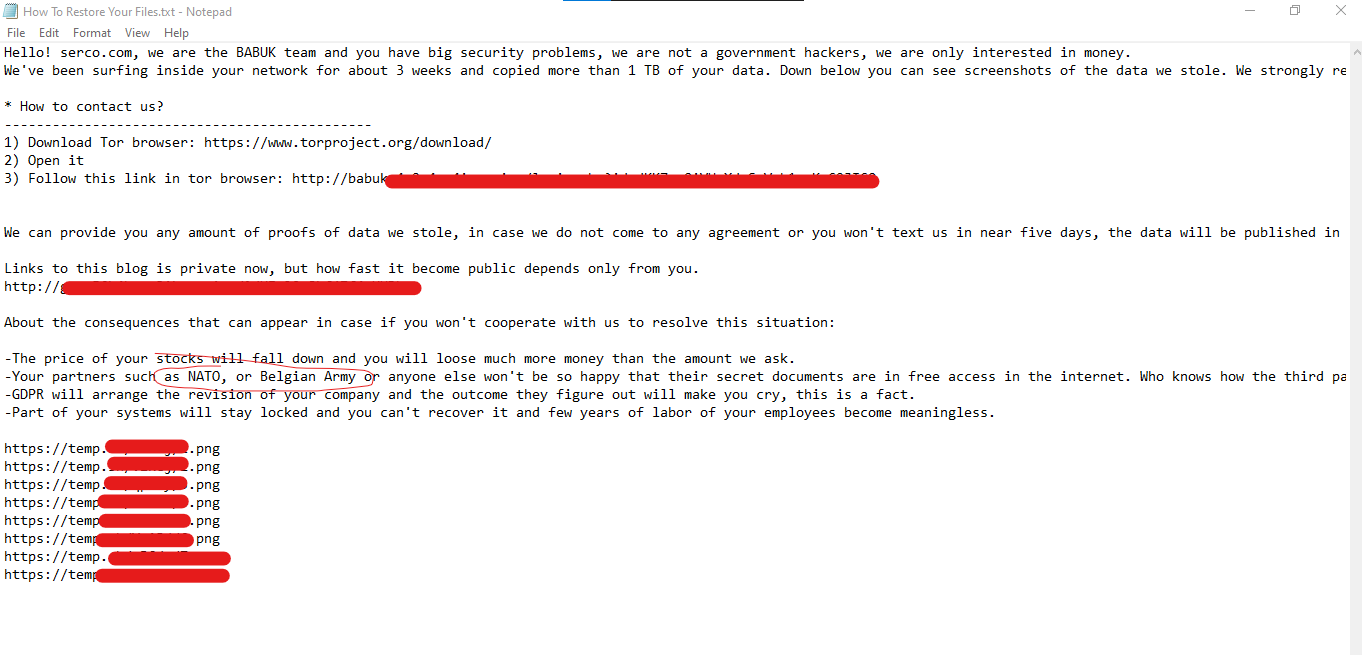
"Hello! http://serco.com, we are the BABUK team and you have big security problems, we are not a government hackers, we are only interested in money. We've been surfing inside your network for about 3 weeks and copied more than 1 TB of your data" gloated the ransomware note.
"We can provide you any amount of proofs of data we stole, in case we do not come to any agreement or you won't text us in near five days, the data will be published in our blog. Links to this blog is private now, but how fast it become public depends only from you... Your partners such NATO or Belgian Army or anyone else won't be so happy that their secret documents are in free access in the internet", the cybercriminals added.
Documents posted by the hackers on their dark web site and seen by The Stack include a non-disclosure agreement between Serco and a company working to support the European Space Agency. Serco makes over £1 billion annually from defence-related operations, running critical support services and sensitive facilities. It is involved in everything from ship modernisation and aircraft maintenance, through to operation of nuclear facilities, "analysis of cyber activity," and the training programmes.
https://twitter.com/HEX_FORENISCS/status/1354833801151733763
As The Stack published, the link in the initial ransomware note had been wiped of documents, suggesting negotiations had opened.
The breach was first reported by Sky News. More to follow.
