
Former NCSC Director of Incident Management John Noble, opening the Qualys Security Conference (QSC) in London, warned that much of what he would say would be “to use a British expression, bleedin’ obvious”.
He was right. And that's a problem.
“My colleagues in the NCSC [say] patching remains the single most important activity that an organisation needs to focus on,” Noble -- now a non-executive director at the NHS -- said, adding: “Poor credential management continues to be a big challenge for organisations – it certainly is within the NHS.”
He noted: “We've had compromises based on poor credential management, where we had people who've left the organisation, [and their] password has been compromised – basic things like that. Password reuse, all of those other aspects, not having multi factor authentication deployed with where it should be.”
Legacy systems, poor due diligence during/post-mergers and acquisitions, cloud configuration errors, poor inventory and asset management – Noble’s list of the most commonly exploited issues will come as no surprise to anyone. But still, organisations are failing to secure the fundamentals of IT infrastructure.
See: The top 3 ransomware infection vectors remain troublingly consistent
One way to solve this problem is to change who owns risk - which was the approach at Sky Betting and Gaming. The firm uses the Spotify model, where internal "tribes" are highly vertically integrated; Glenn Pegden, security vulnerability manager at Sky Betting, said that when their CISO arrived, he gave ownership of security risks to the tribes.
"The model we've got the tribes own everything else end to end. They're responsible for availability, they're responsible for design. They are now responsible for security risks. And it changed us from being a blocker, the typical security policeman that goes no you can't do that, to facilitators," said Pegden at the conference.
"We didn’t make decisions on whether stuff went live any more - basically, the tribes could put live whatever they wanted. We’ll advise on the risk, we'd say we think that there is a risk you probably don't want to carry, but ultimately it's your risk not ours – yours."
He said this had revolutionised the role of the security team: "The second we pushed the risks back to the tribe and stopped managing, engaging that risk for them, it opened up a whole new pile of opportunities for us."
Automating patching, improving risk management

For many organisations, such a radical move is almost certainly not practical.
And for these organisations Sumedh Thakar, CEO and president of Qualys, believes increasing the role of automation, and moving from vulnerability management to risk mitigation, is the future.
He told QSC: “What we hear from a lot of the customers is about figuring out ways to really focus on what is the risk – it is pointless to look at your five million vulnerabilities that are constantly getting reported.
“It is which of those are truly causing risk to the organisation and how do we move from a model today where it is a very blanket, ‘you have to fix everything that is level three and above’, more to a risk-based approach.”
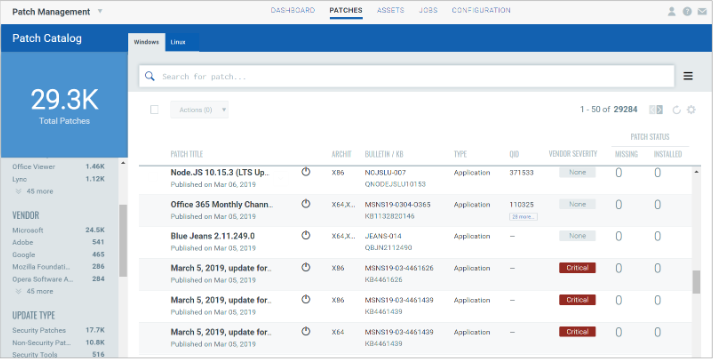
(Qualys provides, among other tools, a Vulnerability Management, Detection, and Response (VMDR) module that lets users discover, assess, and prioritise patches for critical vulnerabilities, automating patch management on Windows and Linux assets using a single patch management application to schedule run-once or recurring jobs
Qualys’s solution to this is automation, an area where Thakar suggests security has lagged behind IT in general in adoption – in contrast to bad actors.
“The attackers are using a lot of automation, right? Well, we struggled to get approval to run a scan from our team, when the attackers don't need to get that permission. They're just doing it whenever they want, right. So it's just it doesn't make any sense. But that's what we deal with,” said Thakar.
Paul Baird, UK chief technology security officer at Qualys, agreed: “We’re behind the curve at the moment. The attackers have got the upper hand because they are automated. They are having fun. You know, it's an amazing business model for them. They can get up make $10 million and go back to bed again.”
Patch management is an area where automation could dramatically reduce organisations’ attack surfaces – but for many it remains a steadfastly manual process.
To some extent this is a function of how important IT has become to organisations, according to Thakar:“The ability of a business to grow is directly proportional today to innovation IT can do within the organisation. And I think so there is by nature a certain amount of risk averseness, and so they sometimes don't want to be in a situation where they tried to do something and then it breaks,” he told The Stack at the QSC event, May 12.
“So infrastructure is exploding, business is growing, but your cybersecurity team, if they're not able to keep up, then you're really getting to the point where the only way you can do this is with a significant amount of automation.”
Follow The Stack on LinkedIn
To Thakar, the way to square this circle is to automate basic security hygiene tasks like much patching.
Thakar said an important step is “getting over the fears of what if something break has to be balanced with the fear of what happens when we get compromised, right?”
He gave one example of this in his keynote, where an organisation was driven not by fear of a breach, but fear of losing business. Having installed the Qualys agent for vulnerability management, the organisation had a debate about whether to use patch management, with nothing getting done – until the pandemic forced 300,000 employees to work from home: “They are a service provider. So all their customers actually require them to provide a monthly patch status report. And they were not able to produce that. So the business came and told them if you're not able to produce this report in two weeks, we're going to lose X million dollars of business.
“Their CISO called me on Monday. By Wednesday, we had it enabled on all 300,000 laptops, patching immediately without any VPN or anything. By Friday, they sent out the patch report. And there was no more conversation about if patching should be done together or not,” said Thakar.
Unfortunately many enterprises are driven by cost allocation decisions that will always prioritise other things: “At times we are challenged and I see that with the NHS - in healthcare it’s a particular problem; every penny you're taking for cybersecurity, you're not spending on patient care. But the reality is this is a patient care issue. Because if we lose access to these systems, we completely undermine people's confidence,” said Noble.