In early April VMware customers were warned to patch a series of critical vulnerabilities. An emergency directive from the US's CISA noted that threat actors managed to "reverse engineer the update and begin exploitation of impacted VMware products that remained unpatched within 48 hours of the update’s release."
On May 18, 2022, VMware patched two new vulnerabilities (CVE-2022-22972 and CVE-2022-22973) that let attackers trigger a server-side template injection that may result in RCE (CVE-2022-22954); escalate privileges to 'root' (CVE-2022-22960 and CVE-2022-22973); and get admin access without authentication (CVE-2022-22972).
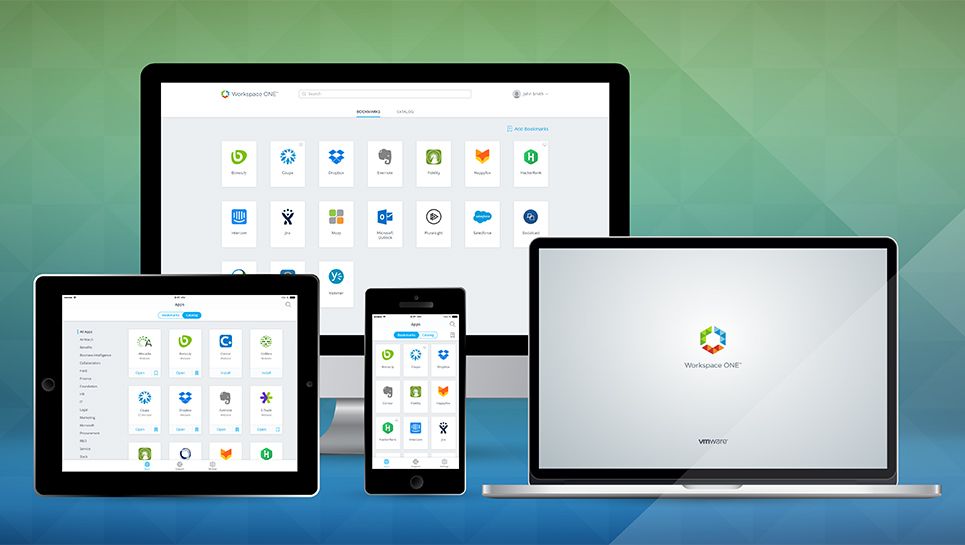
Now the security team at San Francisco-based company Horizon3 say that they have successful reproduced exploitation of CVE-2022-22972 affecting multiple #VMware products such as Workspace ONE with security researcher James Horseman at the company expected to share a technical writeup and proof-of-concept (POC) shortly.
US federal agencies were told to find, mitigate, and report all affected instances by May 24.
New VMware Workspace ONE vulnerabilities: Patch urgently (again)
Admins who have overlooked the fact that May 18's advisory related to brand new critical (CVSS 9.8) vulnerabilities in a product that they had just patched should mitigate or patch urgently, security professionals say; exploitation is once again expected to rapidly follow.
(The security researcher who found April's VMware ONE vulnerabilities, Steven Seeley told The Stack via DM last month that ~1,000 VMware instances were showing up as publicly exposed, adding: “This is a system that holds the keys – it manages user access and identity which means if this is comprised, then an attacker can very easily pivot the attack further by obtaining those keys” adding “the template injection bug is not complex..."
The vulnerability appears to require local domain access to one of the following:
- VMware Workspace ONE Access (Access)
- VMware Identity Manager (vIDM)
- VMware vRealize Automation (vRA)
- VMware Cloud Foundation
- vRealize Suite Lifecycle Manager
But from there escalation to full takeover is understood to be trivial. Mitigation details are here.
In other security news, CISA late May 24 added 20 new vulnerabilities to its Known Exploited Vulnerabilities Catalog, based on evidence of active exploitation. Security teams should check for exposure.
