Router and networking technology specialist NETGEAR has pushed out a hefty 48 security advisories in the past three days, as it patches a raft of bugs including a nasty looking (CVSS v3 9.8) pre-authentication command injection vulnerability in its NMS300 network management system (product sheet: "insight into network elements, including third-party devices.")
Other issues include the following products* spilling admin credentials to the potentially malicious in another critical bug (CVSS v3 Score: 9.6)
- CBR40, running firmware versions prior to 2.5.0.10
- RBK752, running firmware versions prior to 3.2.15.25
- RBR750, running firmware versions prior to 3.2.15.25
- RBS750, running firmware versions prior to 3.2.15.25
- RBK852, running firmware versions prior to 3.2.10.11
- RBR850, running firmware versions prior to 3.2.10.11
- RBS850, running firmware versions prior to 3.2.10.11
NETGEAR security updates span a sprawling product portfolio of routers, more.
Also of note amongst the flurry of fixes, a CVSS 9.3 "authentication bypass" bug affecting a sprawling product range of routers, including:
- D6200, running firmware versions prior to 1.1.00.36
- D7000, running firmware versions prior to 1.0.1.74
- PR2000, running firmware versions prior to 1.0.0.30
- R6020, running firmware versions prior to 1.0.0.42
- R6050, running firmware versions prior to 1.0.1.22
- JR6150, running firmware versions prior to 1.0.1.22
- R6080, running firmware versions prior to 1.0.0.42
- R6120, running firmware versions prior to 1.0.0.66
- R6220, running firmware versions prior to 1.1.0.100
- R6230, running firmware versions prior to 1.1.0.100
- R6260, running firmware versions prior to 1.1.0.64
- R6700v2, running firmware versions prior to 1.2.0.62
- R6800, running firmware versions prior to 1.2.0.62
- R69002, running firmware versions prior to 1.2.0.62
- WNR2020, running firmware versions prior to 1.1.0.62
*Note: a great many other NETGEAR products are affected by other bugs of varying severity. Firmware updates are available. Get y'selves a'patchin'.
NETGEAR has an active bug bounty programme with Bugcrowd.
The company adds in its advisory: "We appreciate and value having security concerns brought to our attention... Being pro-active rather than re-active to emerging security issues is fundamental for product support at NETGEAR." Found more bugs? You can report them here.
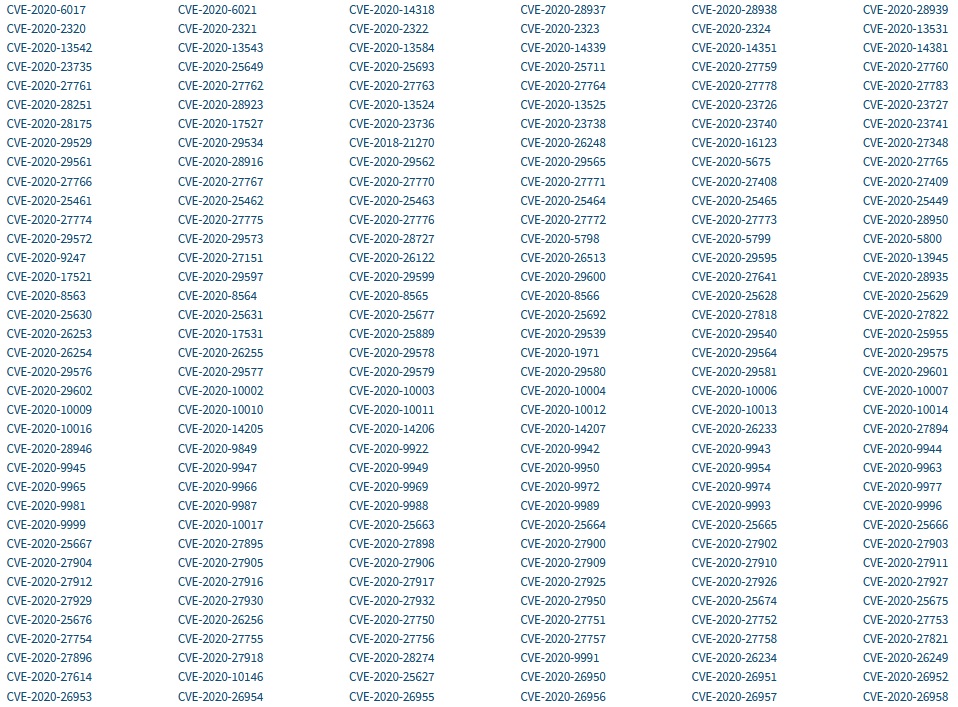
A tidal wave of software security vulnerabilities in general shows no signs of slowing. In 2016 just 5,579 bugs were allocated CVEs (identifiers for cybersecurity vulnerabilities). By 2019 the figure had hit 13,988. It is on track to climb over 20,000 in 2020. NIST's National Vulnerability Database shows some 900 bugs were allocated CVEs this December alone.
See also: We got hit by ransomware. This is how it played out.
p.s. Why the pumpkins? We put "patch" into Unsplash.com Sometimes you've just got to roll with things. Better than another hooded hacker, right? Image credit: https://unsplash.com/@jlynch









