From March 2023, all standalone cyber insurance policies underwritten by members of the sprawling Lloyd’s of London marketplace “must exclude liability for losses arising from any state-backed cyber attack” the 300-year-old organisation has warned – telling members that cyber attack coverage “if not managed properly… has the potential to expose the market to systemic risks that syndicates could struggle to manage.”
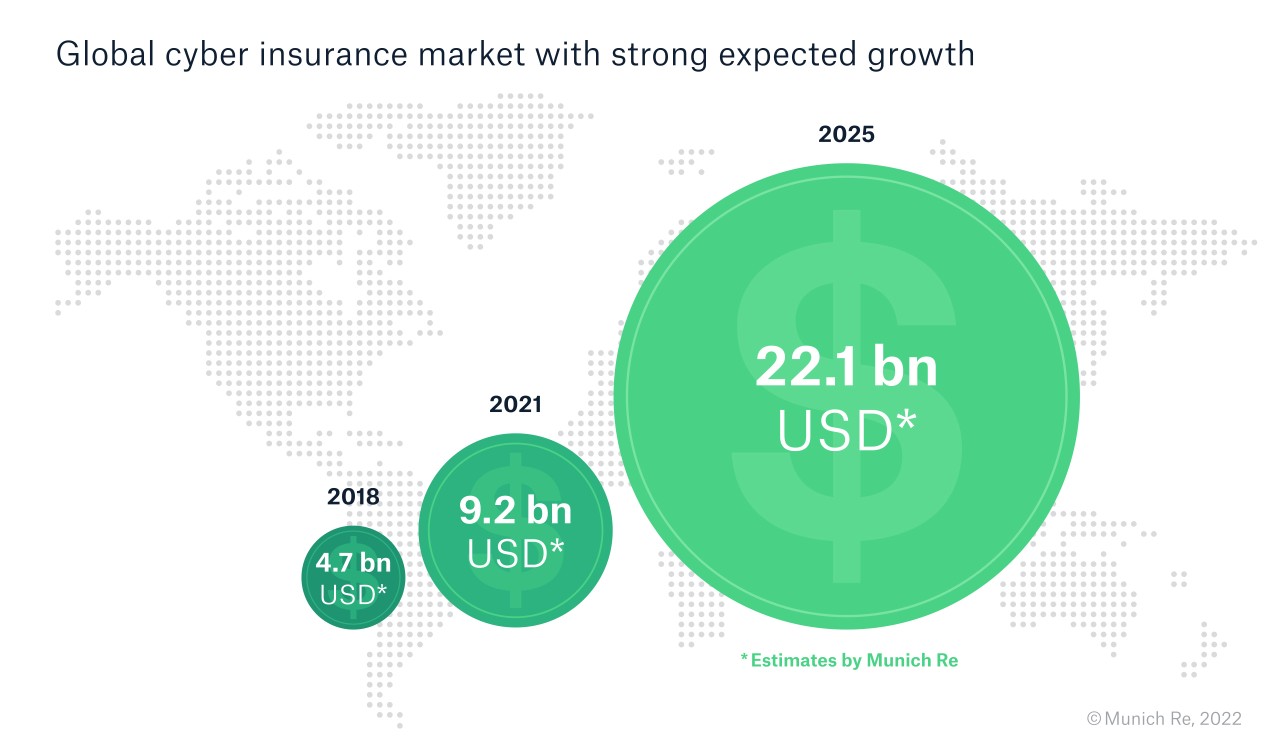
The move comes as appetite for cyber insurance continues to grow. Underwriter Munich Re said it saw cyber premiums worldwide at $9.2 billion at the beginning of 2022 and estimated that they will reach a value of approximately $22 billion by 2025, with customers typically wanting "coverage to extend to data recovery services in an emergency, a 24-hour hotline, legal advice and forensic services [and preventative services] in the area of network security, backup and password management" -- as its data and market surveys showed.
Lloyds members – spanning 50 leading insurance companies, over 350 registered brokers and a global network of over 4,000 cover holder offices – pay out more than £57,031 in claims per minute. With cyber attacks continuing to be rampant, attack surface growing as organisations roll out more applications, write more code, hire more remote works, and connect more physical systems to networks, the risk for insurers is clear.
“The ability of hostile actors to easily disseminate an attack, the ability for harmful code to spread, and the critical dependency that societies have on their IT infrastructure, including to operate physical assets, means that losses have the potential to greatly exceed what the insurance market is able to absorb,” Lloyds said.
State-backed cyber-attack exclusion must, at minimum, Lloyd’s said on August 18, (as truncated by The Stack):
- Exclude losses arising from a war (whether declared or not)
- Exclude losses arising from state-backed cyber attacks
- Be clear as to whether cover excludes computer systems located outside the target state
- Set out a robust basis for attribution
- Ensure all key terms are clearly defined
The guidance comes nine months after Lloyds also published four draft cyber insurance contract clauses for its members to include in standalone cyber insurance contracts that exclude all losses caused by war. (Those November 2021 Cyber War and Cyber Operation Exclusions meet the newly-announced requirements, Lloyd’s noted, so members who already worked them into policies need not specifically take further action…)
The insurance marketplace notes that Lloyd’s role is to support a competitive and resilient cyber insurance market and in this bulletin it has not mandated clauses for managing agents, emphasising that rather than applying a ‘one size fits all’ approach to the risk in question, the guidance issued this month "encourages managing agents to recognise and apply due diligence to the specific complexities around state-sponsored cyber attacks."

For those wondering about attribution, the war exclusions emphasise that “the primary but not exclusive [our italics] factor in determining attribution of a cyber operation shall be whether the government of the state (including its intelligence and security services) in which the computer system affected by the cyber operation is physically located attributes the cyber operation to another state or those acting on its behalf”.
Such attribution is a rarity after ransomware attacks and will become even more challenging as ransomware groups rebrand; expect much ongoing industry debate over the fine print of attribution in policy renewals and a plethora of different approaches to attribution to continue, with little standardisation yet.
The Stack published its critical view on that guidance at the time here, writing as risk appetite for cyber insurance coverage had already plunged among insurers and premiums had soared. (Risk Placement Services Inc., a unit of Arthur J. Gallagher & Co., noted October 5 that “insurers that were more than eager to issue $5 million cyber liability policies last year have scaled back to limits of $1-3 million in 2021, even on renewals… building a cyber liability coverage tower has become more challenging”. By mid-2022 that trend had eased, market watchers say, with insurance advisor WTW noting in July that “clients still need to show good level of risk control in order to secure capacity, however insurers are increasingly demonstrating flexibility where clients can provide the necessary context to explain their risk acceptance rationale. Insurers will have particular areas of focus and clients will need to demonstrate strong control measures in those areas. Unsurprisingly Insurers are keen to understand the business impact of events such ransomware attacks and extortion demands…”)
Lloyd’s move comes as the insurance world has continued to struggle with optimising cybersecurity coverage.
As ALM Research recently noted: “Every year over the past decade, accelerated dramatically by the pandemic, has seen higher numbers of cybersecurity insurance claims accompanied by skyrocketing payouts.
"Insurers have responded by focusing on the products: on limiting coverage, raising rates and changing underwriting standards” – with the market intelligence firm noting that “insurers are uniquely placed to build information coalitions of clients, insurers, brokers, technology firms and public sector players for data- sharing to better understand cyber events as well as the impact of good cybersecurity planning and strategy.
The state of the market means that there is real opportunity for innovators however: “While there is a certain amount of panic in cybersecurity insurance markets, some view the current pricing and coverage challenges as a market shakeout of inexperienced insurers who treated cybersecurity as just another P&C line, providing an opportunity for those willing to commit and invest in the necessary expertise and resources to specialize…”
Background points:
As Paul Brucciani, cybersecurity Advisor, WithSecure, notes to The Stack.
"The cyber insurance market is hardening. Companies seeking cyber insurance should look at it as a source of emergency finance to pay for specialist technical and professional services support.
"Companies can significantly reduce their cyber security risk by doing the following:
- Make those responsible for managing risk define the cyber risk management strategy
- Conduct regular, phishing awareness training
- Mandate multi-factor authentication to access network resources
- Use only password manager-generated passwords
- Maintain an inventory of IT assets and patch them regularly, to minimize your attack surface
- Impede attackers with proactive detection and response controls
- Rehearse what you would do when a security incident happens.’
Lloyds meanwhile says that "cyber remains a priority area for Lloyd’s. The advisory guidance provided this week, following consultation with our market, is to ensure we take on the right kinds of risk as a market while approaching this complex field with the expertise and diligence it requires. We will continue to take a pragmatic and innovative approach to supporting the growth of cyber at Lloyd’s" it added in an emailed comment.








