
Microsoft is investigating claims the criminal gang Lapsus hacked an internal Microsoft Azure DevOps account, which the group posted a screenshot from on Sunday March 20.
Lapsus posted, then swiftly deleted, the screenshot on its Telegram channel, saying “Deleted for now will repost later”. The screenshot, which was saved before deletion by several observers in the Telegram channel, appears to show the contents of an Azure DevOps account belonging to a Microsoft worker.
From what can be seen on the screenshot, the account has access to a number of Bing-related projects, including Bing engineering projects run by Microsoft’s Silicon Valley office, along with the Bing source code and front end. The projects are listed alphabetically, so this may not reflect the full extent of the account’s access.
A Microsoft spokesperson told The Stack: “We are aware of the claims and are investigating.”
UPDATED March 22: Lapsus$ later leaked source code for Bing, Cortana, and over 250 other projects. Bleeping Computer reports that "some of the leaked projects contain emails and documentation that were clearly used internally by Microsoft engineers to publish mobile apps." Microsoft declined further comment.
If confirmed, the incident would come 13 months after Microsoft admitted that the attackers behind the SolarWinds attack breached certain Microsoft code repositories and stole proprietary source code including details about how Azure authenticates customers. (That campaign came in the wake of the landmark SolarWinds supply chain attack that which Microsoft earlier said bears the fingerprints of a stunning 1,000+ developers.)
See also: The top three ransomware infection vectors
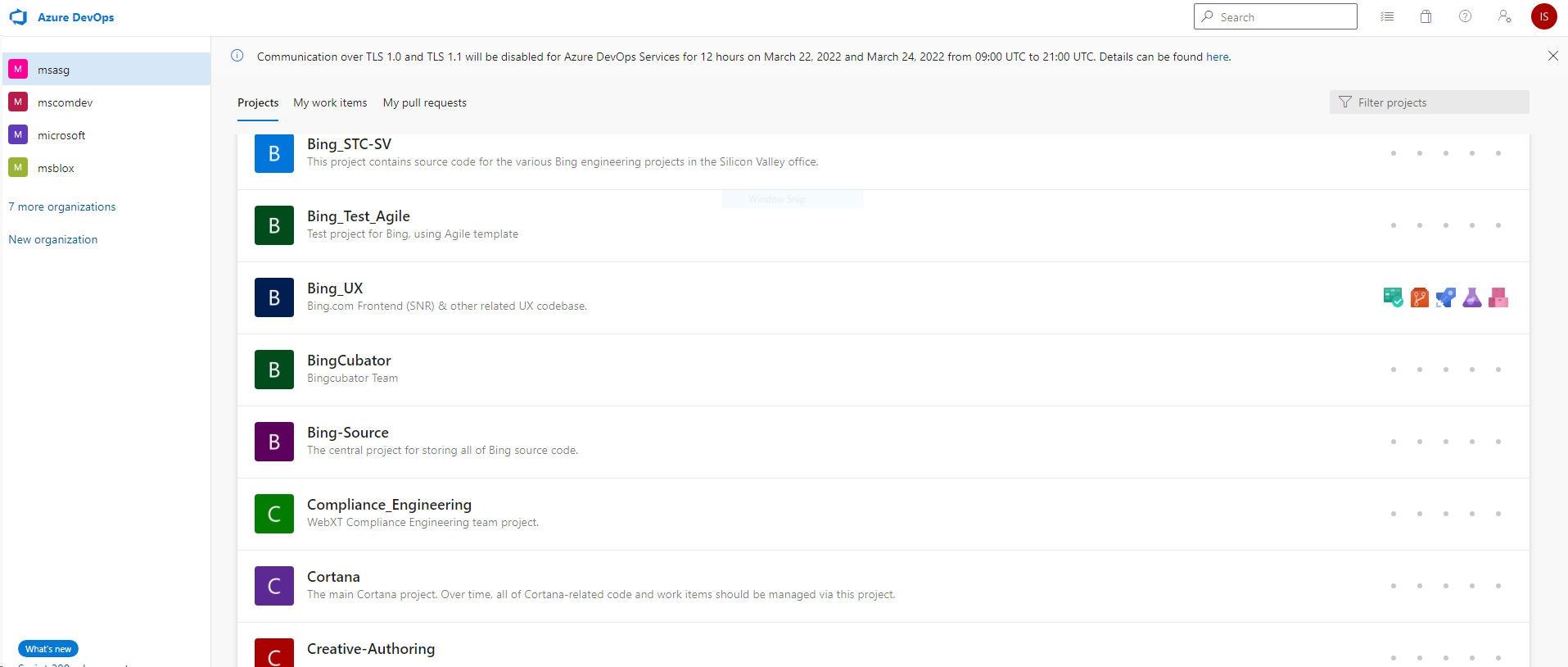
Commentators in the infosec community were divided on the likelihood that Lapsus hacked Microsoft, with some noting a screenshot such as this could be easily faked. Others speculated Lapsus may have removed the screenshot as it revealed the initials of the purported account owner.
The Lapsus (or Lapsus$) hacking group has successfully breached major organisations including Samsung, Nvidia and Ubisoft, after making its start attacking Portuguese-language targets in Brazil and Portugal.
The group has actively advertised for insiders as it seeks VPN access and other additional network administration privileges to infiltrate organisations. Other TTPs do not appear to have been reported in detail yet by the threat intel community but per recent NCSC reports, the tried and tested trio of spearphishing, brute-forcing exposed RDP and exploiting unpatched software remains effective for initial early breaches.
Earlier this month the gang announced it was targeting insiders in major tech firms.
Cybersecurity professionals have been warning about the dangers of insider attacks for some time, with Siemens USA CSO Kurt John among those warning of the risk at a panel last month.
When the group breached Nvidia, it stole a terabyte of internal data, including designs for graphics cards, source code, and usernames and passwords for more than 70,000 Nvidia employees. In a variation of normal requests for money, Lapsus demanded Nvidia remove a cryptomining blocking feature from its GPUs, along with drivers for its chips.