A critical Azure Active Directory vulnerability (CVE-2021-42361) left user credentials stored in easily accessible plain text – a bug that could have let attackers make themselves a contributor to the affected Azure AD subscription, creating, managing and deleting resources across the cloud-based IAM service; which, abused, hands a potentially terrifying amount of control to any bad actor who's gained access.
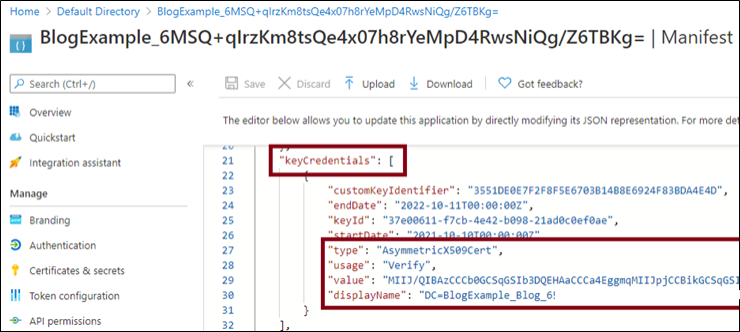
The Azure Active Directory vulnerability resulted in private key data being stored in plaintext by four key Azure services in the keyCredentials property of an Azure AD application. (The keyCredentials property is used to configure an application’s authentication credentials. It is accessible to any user or service in the organization’s Azure AD tenant with read access to application metadata, Microsoft noted in its write-up.)
Azure Automation, Azure Migrate, Azure Site Recovery and Azure applications and Service Principals were all storing their private keys visibily in the public property Microsoft admitted.
Follow The Stack on LinkedIn
“Automation Account 'Run as' credentials (PFX certificates) were being stored in cleartext, in Azure Active Directory (AAD). These credentials were available to anyone with the ability to read information about App Registrations (typically most AAD users)” said attack surface management specialist NetSPI.
The bug was spotted and reported by security firm NetSPI’s practice director Karl Fosaaen.
(His technically detailed write-up can be seen here.)
Microsoft gave it a CVSS score of 8.1 and patched it on November 17 in an out-of-band security update.
Impacted Azure services have now deployed updates that prevent clear text private key data from being stored during application creation, and Azure AD deployed an update that prevents access to private key data that has previously been stored. NetSPI's Fosaaen warned however that "although Microsoft has updated the impacted Azure services, I recommend cycling any existing Automation Account 'Run as' certificates. Because there was a potential exposure of these credentials, it is best to assume that the credentials may have been compromised."
There's no evidence that the bug has been publicly exploited and it would require basic authorisation, but for a motivated attacker it would have represented a significant weapon in their cloud-exploitation arsenal and raises questions about QA at Microsoft given the critical nature of the exposure.
Microsoft described the Azure Active Directory vulnerability in its security update as "an information disclosure vulnerability [that] manifests when a user or an application uploads unprotected private key data as part of an authentication certificate keyCredential on an Azure AD Application or Service Principal....
"This vulnerability allows a user or service in the tenant with application read access to read the private key data that was added to the application" it added.
In a separate blog by Microsoft Security Response Center the company noted that "access to private key data can lead to an elevation of privilege attack by allowing a user to impersonate the impacted Application or Service Principal" -- something illustrated and automated by NetSPI’s Karl Fosaaen.
It's not Azure's first serious security issue this year: security researchers at Israel's Wix in August 2021 found a critical vulnerability in its flagship CosmosDB database that gave them full admin access for major Microsoft customers including several Fortune 500 multinationals. They warned at the time that the "series of flaws in a Cosmos DB feature created a loophole allowing any user to download, delete or manipulate a massive collection of commercial databases, as well as read/write access to the underlying architecture of Cosmos DB."








